Return on Investment

|
I (Fyodor) wrote this story as a chapter of Stealing the Network: How to Own a Continent. In this book, I teamed with FX, Joe Grand, Kevin Mitnick, Ryan Russell, Jay Beale and several other hackers to write individual stories that combine to describe a massive electronic financial heist. While the work is fiction, we tried to portray realistic attacks and technology. For example, my character Sendai uses Nmap, Hping2, Ndos, and similar tools to exploit network configuration and software vulnerabilities commonly found in the wild. Many thanks to Syngress for allowing me to post this online for free. Update: Syngress has released a sequal: Stealing the Network: How to Own an Identity. While Fyodor isn't a co-author of this one, Syngress let him post his favorite chapter online for free. That chapter is Bl@ckTo\/\/3r, by Nmap contributor Brian Hatch. Translations: |
Sendai's Story
Like many professional penetration testers, Sendai was not always the wholesome “ethical hacker” described in his employer's marketing material. In his youth, he stepped well over the line between questionable (grey hat) and flat-out illegal (black hat) behavior. Yet he never felt that he was doing anything wrong. Sendai did not intentionally damage systems, and was only trying to learn more about UNIX, networking, security, phone systems, and related technology. Yet the law might consider some of his actions to be unauthorized access, theft of services, wire fraud, copyright infringement, and trade secret theft. In the rare times that Sendai thought of this, he found solace in the words of the Mentor's Hacker Manifesto: “Yes, I am a criminal. My crime is that of curiosity.” Surely his innocent motives would prevent prosecution. Besides, his teenage arrogance assured him that the government and targeted corporations were too dumb to catch him.
This perception changed dramatically in 1989 and 1990 when the “Operation Sundevil” raids took place. Well-known security enthusiasts, including The Prophet, Knight Lightning, and Erik Bloodaxe, were raided and many more were indicted. The popular Phrack e-zine was shut down while its editor faced trial. Sendai worried that he, too, might be swept up in the persecution. After all, he had been active on some of the same bulletin boards as many suspects, performing similar activities. Sendai was never targeted, but those nine months of stress and paranoia changed his outlook on hacking. He was not exactly scared straight, but he ceased treating network intrusion as a game or casual hobby. In the following years, Sendai became much more disciplined about hiding his tracks through multiple layers of indirection, as well as always wiping logs, even when it was inconvenient. He also began to research his targets and methods much more extensively. Failing to fully understand a system could cause him to miss important defenses and lead to detection. A side effect of this more methodical approach to hacking is that Sendai substantially broadened his network security knowledge and skill set.
Sendai did not recognize the growing value of this skill set and clean record until he was offered the “ethical hacking” job at a well-known auditing firm. The burgeoning Internet was creating such intense demand for security professionals that the firm asked few questions about his past. Using his real name, they were unaware that he even used the hacker handle Sendai. He did have some reservations about commercializing his hobby, not wanting to be seen as a sell out. Despite these concerns, Sendai accepted the position immediately. It sure beat his previous technical support day job! Soon he was living in the security world during both days and nights. The job provided legitimate access to exciting enterprise technologies, and he could hone his hacking skills without risking arrest. Bragging about his exploits led to bonuses instead of jail time. Sendai had so much fun cracking into systems for money that he eventually ceased much of his nocturnal black hat network exploration.
Playing the Market
Sendai's new position pays far more money than his modest lifestyle requires. After tiring of watching the money stagnate in his checking account, Sendai opens a brokerage account and begins to dabble in investing. As with hacking, Sendai learns everything he can about investing. Interestingly, he finds many parallels between the two disciplines. Many books and articles suggest filling a portfolio with funds that passively track broad indexes such as the S&P 500. This insures diversity and reduces the risk of bad timing or stock-picking mistakes. Sendai discards this advice immediately. It sounds too much like the conventional wisdom that computer and telephone users should restrict themselves to advertised behavior, and stay ignorant about how the systems work. Sendai prefers stretching system capabilities to extract as much value as possible, based on a comprehensive understanding. In other words, he wants to (legally) hack the financial markets.
Sendai soon discovers another aspect of investing that is familiar to him. Successful active trading is all about obtaining relevant information before it is widely recognized and reflected in the stock price. This is similar to the security market, where the value of an exploit degrades quickly. The Holy Grail is a zero-day exploit, meaning one that is not publicly known or patched. Attackers who possess such an exploit can break into any system running the vulnerable service. The attack is unlikely to be detected, either, because administrators and IDS systems are not watching for what they do not know exists. Once the vulnerability is published and a patch is created, the exploit value decreases rapidly. The most secure installations will quickly upgrade to be invulnerable. In the coming days and weeks, most organizations will patch their systems. Soon, only the least security conscious networks will be exploitable, and they are probably vulnerable to many other attacks anyway. As other hackers (and in many cases worms) compromise the remaining vulnerable systems, the exploit value continues to dwindle.
In the security world, Sendai sometimes gains zero-day knowledge through friends in the scene and private mailing lists or IRC/SILC channels. Other times, he finds them himself by auditing software for bugs. Auditing produces the best zero-day exploits because the bugs are exclusively his, until he discloses them (or they are independently discovered elsewhere). To find an impressive and generally useful vulnerability, Sendai tends to look at widely deployed and frequently exploitable software like Microsoft's IIS webserver, Sendmail smtpd, OpenSSH, or the ISC BIND DNS server. In the more common case that Sendai wants to break into a specific company, he looks for the most obscure software run on the target network. This specialized software is unlikely to have gone through the rigorous testing performed against more popular packages. An alternative approach to obtaining zero-day is to buy it from the controversial organizations that openly broker such information. Sendai has never resorted to this, for both ethical and financial reasons. He still believes some information wants to be free.
The flow of valuable investment insights is similar to security information. Someone with the right insider connections or a willingness to pay extravagant fees to research boutiques can learn information before it moves the market. Unable to partake in these options, Sendai decides to do his own research. Some of the most valuable preannouncement data are company earnings and mergers, acquisitions, or big partnerships. After a couple hours of brainstorming, Sendai comes up with several ways to use his security and networking expertise to his advantage.
Information Leakage at the Packet Level
Because Sendai cannot think of above-board ways to learn public companies' private earnings information directly, he looks for attributes that may correlate strongly with earnings. One idea is to study the SSL traffic to e-commerce sites. The amount of encrypted traffic they generate is often proportional to the number of sales during that period. This begs the next question: How will Sendai measure a company's SSL traffic? They certainly will not tell him. Breaking into a router barely upstream of the target host would give him access to this data, but that is quite illegal and also requires substantial custom work for each target. Sendai wants a general, unobtrusive, easy, and legal way to determine this information.
Eventually, Sendai thinks of the fragmentation ID field in Internet Protocol (IP) packets. This unsigned 16-bit field is intended to provide a unique ID number to each packet sent between machines during a given time period. The primary purpose is allowing large packets, which must be fragmented during transit, to be reassembled properly by the destination host. Otherwise a host receiving hundreds of fragments from dozens of packets would not be able to match fragments to their original packets. Many OS developers implement this system in a very simple way: they keep a global counter and increment it once for each packet sent. After the counter reaches 65,535, it wraps back to zero.
The risk of this simple implementation is that it allows bad guys to remotely determine traffic levels of a host. This can be useful for many sinister purposes, including an extraordinarily stealthy port scanning technique known as Idle Scan. Sendai will use it to estimate daily orders.
He decides to test whether popular public e-commerce sites are actually vulnerable to this sort of information leakage. He visits the online sites of Dell and Buy.Com, following the order placement path until reaching their secure sites. These sites are designated by the https protocol in the URL bar and a closed padlock icon on his browser. They are ecomm.dell.com and secure.buy.com. Sendai uses the open source hping2 program (freely available from www.hping.org ) to send eight TCP SYN packets, 1 second apart, to port 443 (SSL) of the specified host.
Using hping2 and the IP ID Field to Estimate Traffic Levels
# hping2 -c 8 -S -i 1 -p 443 ecomm.dell.com HPING ecomm.dell.com (eth0 143.166.83.166): S set, 40 headers + 0 data bytes 46 bytes from 143.166.83.166: flags=SA seq=0 ttl=111 id=8984 rtt=64.6 ms 46 bytes from 143.166.83.166: flags=SA seq=1 ttl=111 id=9171 rtt=62.9 ms 46 bytes from 143.166.83.166: flags=SA seq=2 ttl=111 id=9285 rtt=63.6 ms 46 bytes from 143.166.83.166: flags=SA seq=3 ttl=111 id=9492 rtt=63.2 ms 46 bytes from 143.166.83.166: flags=SA seq=4 ttl=111 id=9712 rtt=62.8 ms 46 bytes from 143.166.83.166: flags=SA seq=5 ttl=111 id=9974 rtt=63.0 ms 46 bytes from 143.166.83.166: flags=SA seq=6 ttl=111 id=10237 rtt=64.1 ms 46 bytes from 143.166.83.166: flags=SA seq=7 ttl=111 id=10441 rtt=63.7 ms --- ecomm.dell.com hping statistic --- 8 packets transmitted, 8 packets received, 0% packet loss # hping2 -c 8 -S -i 1 -p 443 secure.buy.com HPING secure.buy.com (eth0 209.67.181.20): S set, 40 headers + 0 data bytes 46 bytes from 209.67.181.20: flags=SA seq=0 ttl=117 id=19699 rtt=11.9 ms 46 bytes from 209.67.181.20: flags=SA seq=1 ttl=117 id=19739 rtt=11.9 ms 46 bytes from 209.67.181.20: flags=SA seq=2 ttl=117 id=19782 rtt=12.4 ms 46 bytes from 209.67.181.20: flags=SA seq=3 ttl=117 id=19800 rtt=11.5 ms 46 bytes from 209.67.181.20: flags=SA seq=4 ttl=117 id=19821 rtt=11.5 ms 46 bytes from 209.67.181.20: flags=SA seq=5 ttl=117 id=19834 rtt=11.6 ms 46 bytes from 209.67.181.20: flags=SA seq=6 ttl=117 id=19857 rtt=11.9 ms 46 bytes from 209.67.181.20: flags=SA seq=7 ttl=117 id=19878 rtt=11.5 ms --- secure.buy.com hping statistic --- 8 packets transmitted, 8 packets received, 0% packet loss
The IP ID fields in both cases show a pattern of steady monotonic increases, which is consistent with trivial packet counting behavior. During this test, the Dell machine sends an average of 208 packets per second (10441 minus 8984 all divided by 7) and secure.buy.com is showing 26 pps. One added complexity is that major hosts like Dell and Buy.Com have many systems behind a load balancer. That device ensures that subsequent packets from a certain IP address go to the same machine. Sendai is able to count the machines by sending probes from many different IP addresses. This step is critical, as the pps rate for a single box will naturally decrease when more machines are added to the farm or vice versa. Against a popular server farm, he may need many addresses, but huge netblocks can easily be purchased or hijacked.
Sendai begins to execute his plan. He writes a simple C program to do the probing and host counting using Dug Song's free libdnet library. It runs via cron a few dozen times a day against each of many publicly traded targets that are vulnerable to this problem. These samples allow an estimation of traffic for each day. Sendai knows better than to jump in with his money right away. Instead he will let his scripts run for a full quarter and count the cumulative traffic for each company. When each company reports results, he will divide their actual revenue for that quarter by his traffic estimate to compute revenue per packet. The second quarter will be a test. He will multiply revenue per packet by his calculated traffic to guess quarterly revenue, and then compare that revenue to the official numbers released later. Companies that prove inaccurate at this point will be discarded. With the remainder, Sendai hopes finally to make some money. He will watch them for a third quarter and again estimate their revenue. He will then compare his estimate to the First Call Consensus. If his revenue estimate is substantially higher, he will take out a major long position right before the earnings conference call. If he estimates a revenue shortfall, Sendai will go short. Obviously he still needs to research other factors such as pricing changes that could throw off his purely traffic-based revenue estimates.
Corrupted by Greed
Although Sendai feels that this plan is legal and ethical, greed has taken over and waiting nine months is unacceptable. He thinks about other market moving events, such as mergers, acquisitions, and partnerships. How can he predict those in advance? One way is to watch new domain name registrations closely. In some mergers and partnerships, a new entity combines the name of both companies. They must register the new domain name before the announcement or risk being beaten to it by domain squatters. But if they register more than a trading day in advance, Sendai may be able to find out early. He obtains access to the .com TLD zone files by submitting an application to Verisign. This gives him a list of every .com name, updated twice daily. For several days, he vets every new entry, but finds nothing enticing. Again, impatience gets the best of him. Sendai decides to cross an ethical line or two. Instead of waiting for a suggestive name, he will create one! Sendai takes a large (for him) position in a small Internet advertising company. A few minutes later he registers a domain combining that company name with a major search engine. The public whois contact information is identical to that used by the search engine company. Payment is through a stolen credit card number, though a prepaid gift credit card would have worked as well. That was easy!
The next morning, the ad company is up a bit on unusually high volume. Maybe Sendai wasn't the first person to use this domain watching strategy. Message board posters are searching to explain the high volume. His heart racing, Sendai connects through a chain of anonymous proxies and posts a message board response noting the new domain name he just “discovered.” The posters go wild with speculation, and volume jumps again. So does the price. A company spokesman denies the rumors less than an hour later, but Sendai has already cashed out. What a rush! If this little episode does not receive much press coverage, perhaps investors of another small company will fall for it tomorrow. Sendai clearly has forgotten the hacker ethic that he used to espouse, and now dons his black hat for profit rather than solely for exploration and learning.
Freed from his misgivings about outright fraud and other illegal methods, Sendai's investment choices widen immensely. For example, his fundamental research on a company would be helped substantially by access to the CEO and CFO's e-mail. He considers wardriving through the financial district of nearby cities with his laptop, antenna, GPS, and a program like Kismet or Netstumbler. Surely some public company has a wide open access point with an identifying SSID. Standard network hacking through the Internet is another option. Or Sendai could extend his domain name fraud to issuing actual fake press releases. Sendai has seen fake press releases move the market in the past. Still giddy from his first successful investment hack, Sendai's mind is working overtime contemplating his next steps.
Sendai has plenty of time to research investments during work hours because pen-testing jobs have been quite scarce now that the dot-com market has collapsed. Sendai is pleased by this, due to the free-time aspect, until one day when the whole security department of his office is laid off. So much for the best job he has ever had. Sendai takes it in stride, particularly because his severance pay adds to the investment pot that he hopes will soon make him rich.
Revenge of the Nerd
While home reading Slashdot in his underwear (a favorite pastime of unemployed IT workers), Sendai comes up with a new investment strategy. A pathetic little company named Fiasco is falsely claiming ownership of Linux copyrights, trying to extort money from users, and filing multibillion dollar lawsuits. Sendai is sure that this is a stock scam and that Fiasco's claims are frivolous. Meanwhile, mainstream investors seem so fixated by the enormous amount of money Fiasco seeks that they lose their critical thinking ability. The stock is bid up from pennies to over $5! Sendai takes out a huge short position, planning to cover when the stock tumbles back down. Since the claims have no merit, that can't take long.
Boy is he wrong! The Fiasco stock (symbol: SCUMX) climbs rapidly. At $9 per share, Sendai receives a margin call from his broker. Being unwilling to take the huge SCUMX loss, Sendai sells all his other positions and also wires most of the balance from his checking account to the brokerage. This allows him to hold the position, which is certain to plummet soon! It rises further. Maybe this is still due to initial uncritical hype. Perhaps the momentum traders are on board now. Maybe some investors know that anti-Linux corporations Microsoft and Sun secretly are funneling money to Fiasco. At $12, Sendai is woken by another early morning margin call and he lacks the money to further fund the account. He is forced to buy back shares to cover his position, and doing so further raises the price of this thinly traded stock. His account value is devastated.
In a fit of rage and immaturity, Sendai decides to take down Fiasco's Web site. They are using it to propagate lies and deception in furtherance of criminal stock fraud, he reasons. Sendai does not consider his own recent stock shenanigans when judging Fiasco.
Web sites are taken down by attackers daily, usually using a brute packet flood from many source machines (known as a distributed denial of service attack). Sendai realizes that much more elegant and effective attacks are possible by exploiting weaknesses in TCP protocol implementations rather than raw packet floods. Sendai has taken down much bigger Web sites than Fiasco's from a simple modem connection. His favorite tool for doing this is a privately distributed application known as Ndos. He reviews the usage instructions.
Ndos Denial of Service Tool Options
# ndos Ndos 0.04 Usage: ndos [options] target_host portnum Supported options: -D <filename> Send all data from given file into the opened connection (must fit in 1 packet) -S <IP or hostname> Use the given machine as the attack source address (may require -e). Otherwise source IPs are randomized. -e <devicename> Use the given device to send the packets through. -w <msecs> Wait given number of milliseconds between sending fresh probes -P Activates polite mode, which actually closes the connections it opens and acks data received. -W <size> The TCP window size to be used. -p <portnum> Initial source port used in loop -l <portnum> The lowest source port number ndos should loop through. -h <portnum> The highest source port number used in loop -m <mintimeout> The lowest allowed receive timeout (in ms). -b <num> Maximum number of packets that can be sent in a short burst -d <debuglevel>
Ndos is one of those tools that has no documentation (other than the usage screen) and is full of obscure parameters that must be set properly. But once the right values are determined from experimentation or actual understanding, it is deadly effective. Sendai starts it up at a relatively subdued packet rate from a hacked Linux box. You can bet that the -P option was not given. The Fiasco Web site is down until the compromised box is discovered and disconnected three days later.
Although his little temper tantrum was slightly gratifying, Sendai is still broke, jobless, and miserable. Only one thing cheers him upthe upcoming annual Defcon hacker conference! This provides the rare opportunity to hang out with all his buddies from around the world, in person instead of on IRC. Sendai worries whether he can even afford to go now. Stolen credit card numbers are not wisely used for flight reservations. Counting the pitiful remains of his checking and brokerage accounts, as well as the remainder of his credit card limit, Sendai scrapes up enough for the trip to Las Vegas. Lodging is another matter. After mailing several friends, his hacker buddy Don Crotcho (a.k.a The Don) offers to share his Alexis Park hotel room for free.
The following weeks pass quickly, with Sendai living cheaply on ramen noodles and Kraft macaroni and cheese. He would like to try more “investment hacking,” but that requires money to start out with. Sendai blames Microsoft for his current condition, due in part to their clandestine funding of Fiasco, and also because he is one of those people who find reasons to blame Microsoft for almost all their problems in life.
A Lead from Las Vegas
Sendai soon finds himself surrounded by thousands of hackers in Las Vegas. He meets up with The Don, who surprisingly has sprung for the expensive Regal loft room instead of the standard cheap Monarch room. Maybe they were out of Monarchs, Sendai thinks. The two of them head to the Strip for entertainment. Sendai wants to take in the free entertainment, though The Don is intent on gambling. Upon reaching the Bellagio, Sendai sees a roulette table and is tempted to bet his last remaining dollars on black. Then he realizes how similar that would be to the Fiasco speculation that landed him in this mess. And as with airline tickets, using a stolen credit card at casinos is a bad idea. Instead, Sendai decides to hang around and watch The Don lose his money. Don heads to the cashier, returning with a huge stack of hundred dollar chips. Shocked, Sendai demands to know how Don obtained so much money. The Don plays it off as no big deal, and refuses to provide any details. After several hours of persistence and drinking, Sendai learns some of the truth. In a quiet booth in a vodka bar, Don concedes that he has found a new client that pays extraordinarily well for specialized telecom manipulation, which is The Don's professional euphemism for phone phreaking.
Given his precarious financial situation, Sendai begs The Don to hook him up with this generous client. Perhaps he needs some of the security scanning and vulnerability exploitation skills that Sendai specializes in. The Don refuses to name his client, but agrees to mention Sendai if he finds a chance. Sendai really cannot ask for anything more, especially after The Don treats him to a visit to one of Vegas' best strip clubs later that night. Don says it reminds him of Maxim's at home in Iceland.
The Call of Opportunity
The following Tuesday, Sendai is sitting at home reading Slashdot in his underwear and recovering from a massive Defcon hangover when the phone rings. He answers the phone to hear an unfamiliar voice. After confirming that he is speaking to Sendai, the caller introduced himself.
“Hello Sendai. You may call me Bob Knuth. The Don informs me that you are one of the brightest system penetration experts around. I'm working on a very important but sensitive project and hope that you can help. I need three hosts compromised over the Internet and an advanced rootkit of your design installed. The rootkit must be completely effective and reliable, offering full access to the system through a hidden backdoor. Yet it must be so subtle that even the most knowledgeable and paranoid systems administrators do not suspect a thing. The pay is good, but only if everything goes perfectly. Of course it's critical that the intrusions are all successful and go undetected. A single slip up and you will feel the consequences. Are you up to this challenge?”
Thinking quickly, Sendai's first impression is not positive. He is offended by the handle “Bob Knuth,” as it was obviously patterned after the world-renowned computer scientist Don Knuth. How dare this arrogant criminal compare himself to such a figure! “His words also sound patronizing, as if he doubts my skills,” Sendai thinks. There is also the question of what Knuth has in mind. He volunteered nothing of his intentions, and for Sendai to ask would be a huge faux pas. Sendai suspects that Knuth may be the vilest of computer criminals: a spammer! Should he really stoop to this level by helping?
Despite this internal dialog, Sendai knows quite well that his answer is yes. Maintaining his apartment and buying food trump his qualms. Plus, Sendai loves hacking with a passion and relishes the chance to prove his skills. So he answers in the affirmative, contingent of course on sufficient pay. That negotiation does not take long. Usually Sendai tries to bargain past the first offer in principle, but Knuth's offer is so high that Sendai lacks the tenacity to counter. He would have insisted on receiving part of the money up front had he not known that The Don has been paid without incident. Knuth sounds extremely busy, so no small talk is exchanged. They discuss the job specifics and disconnect.
Initial Reconnaissance
Sendai first must perform some light reconnaissance against the three hosts Knuth gave him. Given the amount of “white noise” scanning traffic all over the Internet, he could probably get away with scanning from his own home IP address. A chill passes through him as he remembers operation Sundevil. No, scanning from his own ISP is unacceptable. He moves to his laptop, plugs an external antenna into the 802.11 card, then starts Kismet to learn which of his neighbors have open access points available now. He chooses one with the default ESSID linksys because users who do not bother changing router defaults are less likely to notice his presence. Ever careful, Sendai changes his MAC address with the Linux command ifconfig eth1 hw ether 53:65:6E:64:61:69, associates with linksys, and auto-configures via DHCP. Iwconfig shows a strong signal and Sendai verifies that cookies are disabled in his browser before loading Slashdot to verify network connectivity. He should have used a different test, as he wastes 15 minutes reading a front-page story about that latest Fiasco outrage.
Sendai needs only a little bit of information about the targets right now. Most importantly, he wants to know what operating system they are running so that he can tailor his rootkit appropriately. For this purpose, he obtains the latest Nmap Security Scanner. Sendai considers what options to use. Certainly he will need -sS -F, which specifies a stealth SYN TCP scan of about a thousand common ports. The -P0 option ensures that the hosts will be scanned even if they do not respond to Nmap ping probes, which by default include an ICMP echo request message as well as a TCP ACK packet sent to port 80. Of course -O will be specified to provide OS detection. The -T4 option speeds things up, and -v activates verbose mode for some additional useful output. Then there is the issue of decoys. This Nmap option causes the scan (including OS detection) to be spoofed so that it appears to come from many machines. A target administrator who notices the scan will not know which machine is the actual perpetrator and which are innocent decoys. Decoys should be accessible on the Internet for believability purposes. Sendai asks Nmap to find some good decoys by testing 250 IP addresses at random.
Finding Decoy Candidates with Nmap
# nmap -sP -T4 -iR 250 Starting nmap 3.50 ( http://nmap.org ) Host gso167-152-019.triad.rr.com (24.167.152.19) appears to be up. Host majorly.unstable.dk (66.6.220.100) appears to be up. Host 24.95.220.112 appears to be up. Host pl1152.nas925.o-tokyo.nttpc.ne.jp (210.165.127.128) appears to be up. Host i-195-137-61-245.freedom2surf.net (195.137.61.245) appears to be up. Host einich.geology.gla.ac.uk (130.209.224.168) appears to be up. Nmap run completed -- 250 IP addresses (6 hosts up) scanned in 10.2 seconds #
Sendai chooses these as his decoys, passing them as a comma-separated list to the Nmap -D option. This carefully crafted command is completed by the three target IP addresses from Knuth. Sendai executes Nmap and finds the following output excerpts particularly interesting.
OS Fingerprinting the Targets
# nmap -sS -F -P0 -O -T4 -v -D[decoyslist] [IP addresses] Starting nmap 3.50 ( http://nmap.org ) [...] Interesting ports on fw.ginevra-ex.it (XX.227.165.212): [...] Running: Linux 2.4.X OS details: Linux 2.4.18 (x86) Uptime 316.585 days [...] Interesting ports on koizumi-kantei.go.jp (YY.67.68.173): [...] Running: Sun Solaris 9 OS details: Sun Solaris 9 [...] Interesting ports on infowar.cols.disa.mil (ZZ.229.74.111): [...] Running: Linux 2.4.X OS details: Linux 2.4.20 - 2.4.22 w/grsecurity.org patch Uptime 104.38 days
As the results scroll by, the first aspect that catches Sendai's eye are the reverse DNS names. It appears that he is out to compromise the firewall of a company in Italy, a Japanese government computer, and a US military Defense Information Systems Agency host. Sendai trembles a little at that last one. This is certainly one of the most puzzling assignments he has ever had. What could these three machines have in common? Knuth no longer appears to be a spammer. “I hope he is not a terrorist,” Sendai thinks while trying to shake thoughts of spending the rest of his life branded as an enemy combatant and locked up at Guantanamo Bay.
Shrax: The Ultimate Rootkit
Sendai looks at the platforms identified by Nmap. This is critical information in determining what type of rootkit he will have to prepare. Rootkits are very platform-specific as they integrate tightly with an OS kernel to hide processes and files, open backdoors, and capture keystrokes. Knuth's demands are far more elaborate than any existing public rootkit, so Sendai must write his own. He is pleased that these systems run Linux and Solaris, two of the systems he knows best.
Rather than start over from scratch, Sendai bases his rootkit on existing code. He downloads the latest Sebek Linux and Solaris clients from www.honeynet.org/tools/sebek. Sebek is a product of the Honeynet Project,[2] a group of security professionals who attempt to learn the tools, tactics, and motives of the blackhat community by placing honeypot computers on the Internet and studying how they are exploited. Sebek is a kernel module used to monitor activity on honeypots while hiding its own existence. Sendai revels in the delicious irony of this white hat tool fitting his evil purposes perfectly. A major plus is that it is available for Linux and Solaris.
Although Sebek serves as a useful foundation, turning it into a proper rootkit requires substantial work. Sebek already includes a cleaner that hides it from the kernel module list, but Sendai must add features for hiding files/directories, processes, sockets, packets, and users from everyone else (including legitimate administrators). The syslog functionality is also compromised to prevent intruder activity from being logged. Sendai adds several fun features for dealing with any other users on the system. A TTY sniffer allows him to secretly watch selected user terminal sessions and even actively insert keystrokes or hijack the hapless user's session.
The TTY sniffer makes Sendai smile, thinking back to those youthful days when he would hack university machines just to pester students and professors. Watching someone type rapidly at a terminal, Sendai would sometimes enter a keystroke or backspace, causing the command to fail. Thinking they made a typo, the user would try again. Yet the typos continued! While the user was wondering why she was having so much trouble typing and starting to suspect that the keyboard was broken, phantom keystrokes would start appearing on the screen. That is quite disturbing in itself, but induces panic when the keystrokes are typing out commands like rm -rf ~ or composing a nasty e-mail to the user's boss! Sendai never actually took these damaging actions, but derived a perverse pleasure from alarming the poor users. He wondered what tech support would say when these users would call and declare that their systems were possessed. Sendai now considers himself too mature for such antics, but implements the terminal reading capability to spy on administrators that he suspects are on to him.
Sendai adds another user manipulation feature he calls capability stripping. Linux process privileges are more granular than just superuser (uid 0) or not. Root's privileges are divided into several dozen capabilities, such as CAP_KILL to kill any process and CAP_NET_RAW to write raw packets to the wire. Sendai's feature removes all these capabilities from a logged-in administrator's shell. He may still appear to be root from the id command, but has been secretly neutered. Attempts to execute privileged operations are rejected, leaving the administrator more frustrated and confused than if Sendai had terminated the session by killing his shell.
The infection vector is another pressing issue. Sebek hides itself in the kernel module list, but the module itself is not hidden on disk. Worse, the system startup process must be modified to load the module, or a system reboot will foil the whole plan. This is acceptable on a honeynet, because there is no other legitimate administrator who would notice changes to the start-up process. It does not meet Sendai's requirements so well. Yet Knuth was very clear that the system must be resilient in the face of reboots. Sendai's solution is to inject his evil kernel module (which he has taken to calling Shrax) into a legitimate kernel module such as an Ethernet driver.[1] This avoids having an extra suspicious binary around and modifying startup files. Additionally, Sendai adds an inode redirection system so that the module appears unmolested once loaded. This should protect Shrax from file integrity checkers such as Tripwire, Aide, and Radmind. Of course it is possible that the Linux targets compiled their kernels without module support, as many administrators still believe that will stop kernel root kits. No problem! Sendai has tools for both forcing a module into a running kernel using just /dev/mem, and for injecting a module into a static kernel image so that it will be executed silently during the next reboot.
There is also the backdoor issue. One option is to simply compile and run an ssh server on some obscure port number like 31,337. A trivial patch will bypass the authentication and give root access when a secret username is given. Shrax is capable of hiding the ssh process (and its children) from other users, as well as hiding the socket so it isn't disclosed by netstat and the like. Despite this, Sendai finds the option unacceptable. Even though hidden within the system, an outsider could find the open backdoor port with Nmap. More importantly, Knuth insisted that he be able to activate the backdoor using a wide variety of protocols and subtle packets. Ssh would require that the target network firewalls permit TCP connections to the chosen port. Such permissive firewalls are unlikely at some of the sensitive organizations Knuth wants to attack.
After further brainstorming, Sendai decides on an in-kernel backdoor rather than relying on external programs such as ssh. For backdoors, this one is pretty advanced. Knuth will be happy that its activation interface is the epitome of flexibility. It puts the system interfaces in promiscuous mode (hiding that fact, of course) and examines every IP packet that comes in, regardless of the destination IP address or protocol. The first data bytes are then compared to an identification string. At first Sendai sets that string to “My crime is that of curiosity,” but then he smartly decides to be more subtle and chooses a random-looking string. If the string matches, the remainder of the packet is decrypted using AES and a configurable key. The result is interpreted as a response method description followed by a series of shell commands to be executed as root. There are also a few special configuration commands for tasks like changing encryption keys, activating the TTY and network password sniffers, and disabling Shrax and removing every trace of it. Sendai is particularly proud of the response method description. This tells Shrax how to send back command responses, which are always encrypted with the shared key. Sendai is quite proud of all the transport methods supported. Of course, straightforward TCP and UDP to a given IP and port is offered. Or the user can have responses sent via ICMP echo request, echo response, timestamp, or netmask messages. ICMP time-to-live exceeded messages are supported, too. The data can be marshaled into a web request and even sent through a socks or http proxy. Sendai's favorite Shrax technique is to use a series of DNS requests falling under a domain controlled by the attacker. Shrax can even be set to poll a nameserver frequently for new commands. Unless the system is completely unplugged, Knuth should be able to find a way to tunnel his data back. Of course, one can choose to execute a command without returning a response. This allows the intruder to do so completely anonymously with a spoofed IP packet.
Yet another unique Shrax feature is that it can transparently pass commands through a chain of rootkits. An attacker can configure the client to go through an initial rooted machine in Romania, then to one in China, then to a web server on the target corporation's DMZ, and finally to an internal database machine. The first hops help the attacker cover his or her tracks, whereas the final one may be necessary because the DB is accessible only from the web server.
Sendai goes all out working on Shrax because he plans to use it for several years to come and to share it with his buddies. If it had been written only for this specific task, he would have likely hacked the targets first and written only the most critical features.
After all this work on Shrax, Sendai is itching to deploy his new baby. He wants to start hacking immediately, but knows better. Considering that military and government sites are involved, attacking from his neighbor's wireless connection would be foolish. Sendai remembers how the authorities tracked down Kevin Mitnick based on a wireless connection from his apartment. And if the police ever show up at Sendai's apartment complex, he will be a prime suspect. Sendai suddenly regrets ordering the license plate HACKME for his vehicle. The police might not even notice a more subtle plate such as SYNACK. Sendai has a number of compromised boxes all over the Internet, but he really wants some machine that is unconnected to him, which he can use once and then discard.
Throwaway Account
Sendai decides to venture outside after all these days writing Shrax. Perhaps a day at the theatre, on the beach, or attending a game would be good for him. Instead, Sendai heads for the annual ASR Cryptography Conference. He cannot afford the presentations, but hopes to gain free schwag at the giant expo. He won a Sharp Zaurus PDA the last time, which is wonderful for warwalking to find open WAPs. Sendai brings it along in case they have wireless access at the conference.
Although ASR does offer free wireless connectivity, they attempt to secure it with 802.1X and PEAP authentication. That major hassle causes lines at the free wired terminals. Although Sendai would have checked his mail over ssh (after verifying server's ssh key) from his Zaurus, he certainly will not do so from the terminal pavilion. Even if he trusted the ASR organizers (which he does not), they are totally exposed for any hacker to plug in a keylogger or defeat the software and install a program to do the same. In that instant, Sendai's expression turns from outrage to a mischievous grin as he recognizes this as a source of throwaway accounts!
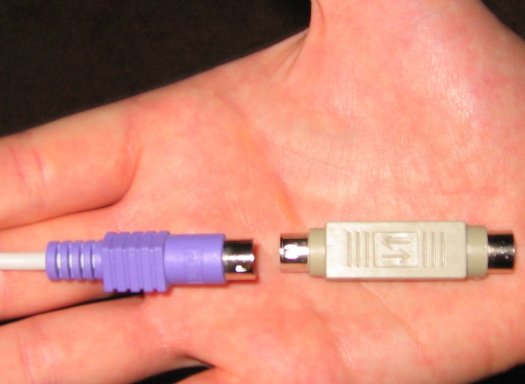
The next morning, Sendai arrives early at ASR to beat the crowds. He takes an available terminal and loads Slashdot. Feigning frustration, he turns to the back of the machine and unplugs the PS/2 keyboard cable. He blows on the PS/2 port behind the machine, while his hands are inconspicuously slipping the KeyGhost SX onto the cable. This tiny device stores up to two million keystrokes and supposedly even encrypts them so that other troublemakers at ASR cannot steal the passwords.[3] Sendai plugs the keyboard cable back in with his little addition, turns back to the front, and resumes web surfing. He smiles to complete his little act that the machine had been broken and is now working again. Darn those dusty keyboard ports! Nobody paid the least attention to him during his charade and he could have been far more blatant without attracting any attention, but it never hurts to be careful. Plus it makes him feel sneaky and clever.
Attaching the Keyghost to Terminal Keyboard Cable
Sendai spends the next few hours at the expo collecting T-shirts, software CDs, pens, a pair of boxer shorts, an NSA pin and bag, magazines, and a bunch of candy treats. After a series of recent Internet worms, many vendors apparently decided that worm-themed giveaways would be clever and unique. Sendai was stuck with gummy worms, refrigerator magnet worms, and a keychain worm. He is tempted to watch the terminals from nearby to ensure nobody steals his $200 KeyGhost. Then he realizes that even if he watches someone discover and take it, he cannot risk a scene by approaching and yelling “Hey! That's my keylogger!” Sendai leaves for a long lunch and then spends a couple hours browsing at a nearby computer superstore.
Late in the afternoon, Sendai returns to ASR, hoping the keylogger remains undetected. He breathes a sigh of relief when it is right where he left it. The terminal is open, so Sendai simply repeats his “broken system” act and 10 minutes later is driving home with all the evidence in his pocket.
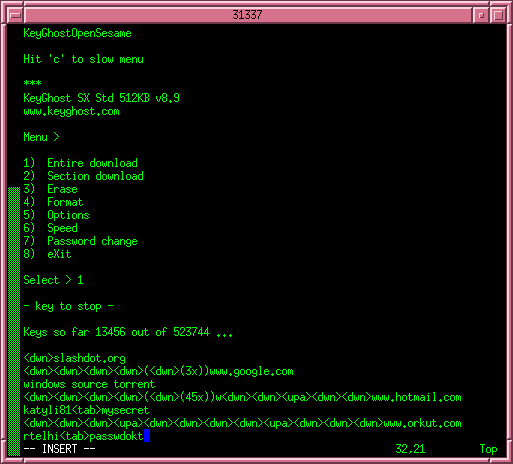
At home, Sendai quickly plugs the Keyghost into his system to check the booty. Sendai opens up the vi editor and types his passphrase. Upon recognizing this code, the KeyGhost takes over and types a menu. Sendai types 1 for “entire download” and watches as pages and pages of text fill the screen. Scrolling through, he sees that the vast majority of users do little more than surf the web. Security sites such as securityfocus.com, packetstormsecurity.nl, securiteam.com, and phrack.org are popular. Many folks made the mistake of checking their Hotmail or Yahoo webmail from the terminals. Sendai has little interest in such accounts. There are also a surprising number of porn sites. No purchases with typed credit card numbers, unfortunately. Search engine queries are interesting. One user searched for “windows source torrent,” another for lsass.exe, and someone else seeks “security jobs iraq.”
Downloading Keyghost Logs
Sendai starts to worry when he passes over half the file without a single remote login. The few people who open terminal sessions only execute simple commands like ls and cat /etc/passwd. Seventy percent into the file, Sendai discovers promising data: A user logged in as antonio via ssh to psyche.ncrack.com. Sendai scans through the following commands, hoping the user will run su and type the password to become the root superuser. There is no such luckAntonio simply reads his e-mail with mutt, sends a note to a coworker describing the conference, then disconnects. In all the excitement of reading keystroke logs, Sendai almost forgets to erase the Keyghost and remove it from his system. If he were to be convicted later based on evidence from his own keylogger, Sendai would be the laughing stock of the criminal hacker community. Such a gaffe reminds him of all the hackers who have been caught based on evidence logged from the packet sniffer they installed on a compromised box.
The keystroke logs contain no further remote system passwords, so Sendai tries to makes the most of psyche.ncrack.com. He moves to the laptop (which is still associated with the linksys WAP) and successfully logs in to Psyche. Now the pressure is on, as he must move fast to avoid detection. His first action is to run the w command to see who else is online. He is relieved that the real antonio is not online, but two other users are. Hopefully they do not notice this suspicious antonio login from an unusual IP address. An attempt by them to chat with the imposter antonio could be a disaster as well. Feeling vulnerable and exposed, Sendai focuses on the task at hand. He runs uname -a to determine that Psyche is running the Linux 2.4.20 kernel. The distribution is Red Hat 9 according to /etc/redhat-release. Sendai immediately thinks of the brk() kernel exploit for kernels up to 2.4.22. That bug was unknown to the public until it was used to compromise many Debian Project machines. Sendai was a little miffed that he had not been in on it during that prepublication 0-day period. It is a very interesting bug, and Sendai had spent two days massaging assembly code into a working exploit. It is about to come in handy. He uploads hd-brk.asm and types:
psyche> nasm -f elf -o hd-brk.o hd-brk.asm psyche> ld -o hd-brk hd-brk.o -Ttext 0x0xa0000000 psyche> ./hd-brk # id uid=0(root) gid=0(root) groups=0(root),1(bin),2(daemon),3(sys),4(adm),10(wheel) #
Despite the hundreds of boxes that Sendai has compromised in his lifetime (legally or not), he never fails to feel a joyful rush of triumph when he first sees that glorious hash prompt signifying root access! But this is still only a minor victory, as the purpose of Psyche is simply to cover Sendai's tracks. There would be no time for celebration even if it was warranted, as there is now a suspicious root shell that other users might notice.
Sendai turns his attention to rootkit installation. The command lsmod shows that the kernel allows modules and that almost 50 of them are installed. This is typical for kernels from major Linux distributions. Sendai injects Shrax into the parport_pc module which, as the name implies, handles PC parallel ports. It is loaded early and unlikely to be changed, meeting the two most desirable attributes. It is also easy to remove and then re-insert the parallel port module without attracting attention. Sendai does so.
With the rootkit seemingly installed, Sendai tests his power. He issues the Shrax hideall command against the sshd process through which he is connected. Suddenly that sshd and all of its descendants (including his rootshell) are now hidden from system process lists. Their syslog messages are ignored and sockets are concealed. Sendai wipes the relevant wtmp, lastlog, and syslog records to remove any trace that antonio logged on this evening. He checks up on the other two logged in users with the TTY sniffer to ensure that they are doing their own thing and not suspecting that anything is remiss. Sendai lightly tests a few complex system components including the compiler gcc and emacs. One of the most common ways attackers are discovered is that they inadvertently break something. The generally attentive Debian folks did not notice intruders until kernel crashes began occurring on several boxes at once. Sendai is glad that no problems have yet appeared with Shrax. A feeling of relief rolls over him as he can now relax. His activities on the system are well hidden now that Psyche is securely 0wn3d.
Seeking the Prize
After all this preparation, Sendai is ready to go after the three primary targets. First he must learn as much as possible about them. He starts with an intrusive Nmap scan. Red Hat 9 comes with Nmap 3.00, which is far out of date. Sendai grabs the latest version from insecure.org, then compiles and installs it into a directory hidden by Shrax. As for the options, Sendai will use -sS -P0 -T4 -v for the same reasons as for his previous scan. Instead of -F (scan the most common ports), Sendai specifies -p0-65535 to scan all 65,536 TCP ports. He will do UDP (-sU) and IP-Proto (-sO) scans later if necessary. Instead of -O for remote OS detection, -A is specified to turn on many aggressive options including OS detection and application version detection. Decoys (-D) are not used this time because version detection requires full TCP connections, which cannot be spoofed as easily as individual packets. The -oA option is given with a base filename. This stores the output in all three formats supported by Nmap (normal human readable, XML, and easily parsed grepable). Sendai scans the machines one at a time to avoid giving the other organizations an early warning. He starts with the Italian company, leading to the following Nmap output.
Nmap Output: A More Intrusive Scan of Ginevra
# nmap -sS -P0 -T4 -v -A -p0-65535 -oA ginevra-ex fw.ginevra-ex.it
Starting nmap 3.50 ( http://nmap.org )
Interesting ports on fw.ginevra-ex.it (XX.227.165.212):
(The 65535 ports scanned but not shown below are in state: filtered)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 3.7.1p1 (protocol 1.99)
Running: Linux 2.4.X
OS details: Linux 2.4.18 (x86)
Uptime 327.470 days
TCP Sequence Prediction: Class=random positive increments
Difficulty=2325858 (Good luck!)
IPID Sequence Generation: All zeros
Nmap run completed -- 1 IP address (1 host up) scanned in 1722.617 seconds
The results show that 22 is the only open TCP port. Sendai is a little disappointed. He was hoping for many more ports, as each is a potential security vulnerability. He notices the line saying that the other 65,535 ports are in the filtered state. That usually means administrators have made an effort to secure the box, since most operating systems install in a default closed state. A closed port returns a RST packet, which tells Nmap that the port is reachable but no application is listening. A filtered port does not respond at all. It is because virtually all the ports were filtered that Nmap took so long (almost half an hour) to complete. Probes against closed ports are quicker because Nmap has to wait only until the RST response is received rather than timing out on each port. A reset response also means that no retransmission is necessary since the probe obviously was not lost. Care clearly was taken to eliminate unnecessary services on this machine as well. Most Linux distributions ship with many of them open. It is also common for small companies to host infrastructure services like name servers and mail servers on the firewall. They do this to avoid placing these public services on a separate DMZ network, but it substantially weakens their security. As a pen-tester, Sendai had compromised many firewalls because they were inappropriately running public BIND nameservers. Apparently Ginevra is smarter than that.
According to Nmap, port 22 is running OpenSSH 3.7.1p1. This is another service that would not be available to the whole Internet in an ideal world, but Sendai can understand why administrators allow it. If something breaks while they are far from home, the admins want to connect from the nearest available Internet service. In so doing, administrators accept the risk that attackers might exploit the service. Sendai intends to do just that. OpenSSH has a sordid history of at least a dozen serious holes, though Sendai does not recall any in this version. Several exploitable bugs in buffer management code were described in CERT Advisory CA-2003-24, but those problems were fixed in 3.7.1. Sendai may have to implement a brute force attack instead. This is often quite effective, though it can take a long time. First Sendai will troll the Internet looking for employee names and e-mail addresses. He will search web pages, USENET and mailing list postings, and even regulatory findings. These will help him guess usernames that may be authorized on fw. He will also try to trick the public company mail server into validating usernames. The username root, of course, will be added to the brute force list.
With a list of users in hand, Sendai will begin the search for possible passwords. He already has a list of the 20,000 most popular passwords out of millions that he has acquired from various databases. Everyone knows words like “secret,” “password,” and “letmein” are common. What used to surprise Sendai is how common profane passwords are. “Fuckyou” is #27 on his list, just above “biteme.” It is also surprising how many people think “asdfgh” is a clever, easy-to-type password that no bad guys will ever guess.
Of course, common passwords differ dramatically based on the organization they are from. So Sendai cannot use just his top password list. He will need to download an Italian language wordlist. Then he will recursively download the entire www.ginevra-ex.it Web site and parse it for new words. Finally, Sendai will whip out Hydra, his favorite open source brute force cracker, to do the actual attack. It may take days, but Sendai is optimistic that he will find a weak password.
Sendai is preparing his plan when he suddenly remembers an obscure vulnerability that affects only OpenSSH 3.7.1p1, and then only when the Pluggable Authentication Modules (PAM) system is in use and privilege separation is disabled. PAM is often used on Linux boxes, so he decides to give it a shot. The vulnerability is laughably easy to exploit. You simply try to login using SSH protocol 1 and any password (except a blank one) is accepted. No wonder that problem did not last long before being discovered and fixed! Sendai crosses his fingers and begins to type.
psyche> ssh -1 root@fw.ginevra-ex.it
The authenticity of host 'fw.ginevra-ex.it (XX.227.165.212)' can't be established.
RSA1 key fingerprint is 2d:fb:27:e0:ab:ad:de:ad:ca:fe:ba:be:53:02:28:38.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added 'fw.ginevra-ex.it,XX.227.165.212' (RSA1) to
the list of known hosts.
root@fw.ginevra-ex.it's password:
#
There is that happy hash prompt again! Sendai will not have to spend days preparing and executing a noisy brute force attack. He does a little root dance, which is similar to what sports players sometimes do when scoring a goal. Nobody is logged onto fw at the time, and the last command shows that people rarely do. So Sendai takes his time cleaning the logs and installing Shrax. He is exceedingly careful not to crash or otherwise break the box, as that sort of blunder could be ruinous.
With one down and two to go, Sendai moves his attention to the Japanese government box. He launches the following intrusive Nmap scan.
An Intrusive Scan of koizumi-kantei.go.jp
# nmap -sS -P0 -T4 -v -A -p0-65535 -oA koizumi koizumi-kantei.go.jp Starting nmap 3.50 ( http://nmap.org ) Interesting ports on koizumi-kantei.go.jp (YY.67.68.173) (The 65535 ports scanned but not shown below are in state: filtered) PORT STATE SERVICE VERSION 113/tcp closed auth Running: Sun Solaris 9 OS details: Sun Solaris 9 Nmap run completed -- 1 IP address (1 host up) scanned in 1791.362 seconds
Oh dear! This host is even worse (from Sendai's perspective) than Ginevra in that it does not even have a single TCP port open! All ports are filtered, except the identd (auth) port, which is closed. Leaving port 113 closed often is done for better interoperability with some (poorly implemented) IRC and mail servers. Even though Sendai cannot connect with closed ports, they improve OS detection accuracy. The lack of open TCP ports will certainly make cracking in more challenging. There must be another way. Sendai considers wardialing the department's telephone number range for carriers, though so many calls to Japan would certainly rack up the long distance charges. Social engineering might work, though that is risky business. UDP scanning is worth a try, though it tends to be slow as sin against Solaris boxes due to their ICMP rate limiting. So Sendai does a UDP scan with the -F option that limits it to about a thousand common ports. No responses are received. This box is locked down tightly. Another idea is IPv6, particularly since this host is in Japan where that protocol is used more frequently than elsewhere. Psyche does not have an IPv6 interface, so Sendai tests this from his laptop using one of the free public IPv6 tunneling services. They provide an IPv6 address and also conceal his originating IPv4 host. Using the -6 option to activate IPv6 mode, Sendai takes another shot at scanning the host.
IPv6 Scan against koizumi-kantei.go.jp
# nmap -6 -sT -P0 -T4 -v -sV -p0-65535 koizumi-kantei.go.jp Starting nmap 3.50 ( http://nmap.org ) Interesting ports on koizumi-kantei.go.jp (2ffe:604:3819:2007:210:f3f5:fe22:4d0:) (The 65508 ports scanned but not shown below are in state: closed) PORT STATE SERVICE VERSION 7/tcp open echo 9/tcp open discard? 13/tcp open daytime Sun Solaris daytime 19/tcp open chargen 21/tcp open ftp Solaris ftpd 22/tcp open ssh SunSSH 1.0 (protocol 2.0) 23/tcp open telnet Sun Solaris telnetd 25/tcp open smtp Sendmail 8.12.2+Sun/8.12.2 37/tcp open time 79/tcp open finger Sun Solaris fingerd 111/tcp open rpcbind 2-4 (rpc #100000) 512/tcp open exec 513/tcp open rlogin 515/tcp open printer Solaris lpd 540/tcp open uucp Solaris uucpd 587/tcp open smtp Sendmail 8.12.2+Sun/8.12.2 898/tcp open http Solaris management console server 4045/tcp open nlockmgr 1-4 (rpc #100021) 7100/tcp open font-service Sun Solaris fs.auto 32774/tcp open ttdbserverd 1 (rpc #100083) 32775/tcp open ttdbserverd 1 (rpc #100083) 32776/tcp open kcms_server 1 (rpc #100221) 32777/tcp open kcms_server 1 (rpc #100221) 32778/tcp open metad 1 (rpc #100229) 32779/tcp open metad 1 (rpc #100229) 32780/tcp open metamhd 1 (rpc #100230) 32786/tcp open status 1 (rpc #100024) 32787/tcp open status 1 (rpc #100024) Nmap run completed -- 1 IP address (1 host up) scanned in 729.191 seconds
Now this is exactly what Sendai likes to see! Many of the services may be unpatched too, since the administrators assumed they were inaccessible. Unfortunately they forgot to firewall IPv6 in the same way they do IPv4. Sendai uses an IPv6-enabled rpcquery command to learn more about the running RPC services, including many that are using UDP. He has several avenues of attack available, but decides on a UDP sadmind vulnerability. Sendai obtains an exploit from H.D. Moore's Metasploit framework (www.metasploit.com), and 10 minutes later is doing the root dance again.
Hacking .MIL
This leaves only one host remaining, and it is certainly the scariest. Hacking Italian and Japanese hosts from the US is one thing. Hacking infowar.cols.disa.mil is quite another. Yet it is too late to stop now. Sendai launches an intrusive scan of the host, and is disappointed to see zero open ports. Not again! This host has no IPv6 address and UDP scans come up negative. Sendai tries some more advanced scan types including Fin scan (-sF), Window scan (-sW), and the ultra-sneaky Idle scan (-sI), all to no avail. He knows Knuth will not accept two out of three, so giving up is no option. Sendai broadens his search, launching an intrusive scan of every host in that 256-host subnet by issuing the command nmap -sS -P0 -T4 -v -A -p0-65535 -oA disanet infowar.cols.disa.mil/24 . That trailing /24 is CIDR notation that tells Nmap to scan 256 addresses. Classless Inter Domain Routing (CIDR) is a method for assigning IP addresses without using the standard IP address classes like Class A, Class B, or Class C.
Upon seeing the results, Sendai grins because many machines are not locked down as tightly as infowar is. Unfortunately, they seem to have their patches in order. During the next day and a half, Sendai finds numerous potential vulnerabilities only to fail in exploitation because the hole is already patched. He is starting to worry. Then he begins to investigate webpxy.cols.disa.mil and discovers a Squid proxy.
A Squid Proxy Is Discovered
Interesting ports on webpxy.cols.disa.mil (ZZ.229.74.191): (The 65535 ports scanned but not shown below are in state: filtered) PORT STATE SERVICE VERSION 3128/tcp open http-proxy Squid webproxy 2.5.STABLE3 Device type: general purpose Running: FreeBSD 5.X OS Details: FreeBSD 5.1-RELEASE (x86) Uptime: 110.483 days
Many organizations maintain a proxy to allow internal clients access to the World Wide Web. They often do this for security reasons, so that material can be scanned for undesirable or malicious content before being provided to the client. It can also keep clients shielded on the internal network so that attackers cannot reach them. Performance and site logging are further reasons managers often prefer this approach. Unfortunately these proxies can do much more harm than good when they are misconfigured. Sendai finds that the Netcat utility (nc) is unavailable on Psyche, so he connects to the proxy with the standard Telnet command and manually types an HTTP CONNECT request.
Open Proxy Test
psyche> telnet webpxy.cols.disa.mil 3128 Trying ZZ.229.74.191 ... Connected to ZZ.229.74.191. Escape character is '^]'. CONNECT scanme.insecure.org:22 HTTP/1.0 HTTP/1.0 200 Connection established SSH-1.99-OpenSSH_3.8p1
Sendai is quite pleased. The proxy allows him to connect to port 22 (ssh) of an arbitrary Internet host and the SSH banner display shows that it succeeded. So perhaps it will allow him to connect to internal DISA machines too! A hacker by the name Adrian Lamo was notorious for publicly breaking into high-profile sites this way. Many companies thanked him for exposing the weaknesses, though the New York Times did not appreciate the unsolicited security help and they pressed charges. Sendai tries to exploit this problem by connecting to port 22 of infowar.cols.disa.mil through the proxy. He had been unable to reach any port on this machine, but through the proxy it works! Apparently he is behind the firewall now. Infowar is running 3.7.1p2, for which Sendai knows of no vulnerabilities. Nor does he have a password, though brute force is always an option.
With the newfound power of his open proxy, Sendai wants to fully portscan infowar and explore the whole department network. He curses the fact that Nmap offers no proxy bounce scan option. Then Sendai remembers a primary benefit of open source. He can modify it to meet his needs. Nmap does offer an ftp bounce scan (-b) that logs in to an FTP server and then tries to explore the network by issuing the port command for every interesting host and port. The error message tells whether the port is open or not. Sendai modifies the logic to connect to a proxy server instead and to issue the CONNECT command. After an afternoon of work, he is proxy scanning likely internal IP ranges such as RFC1918-blessed 192.168.0.0/16 and 10.0.0.0/8 netblocks, looking for internal machines. He finds a whole intranet under the 10.1 netblock, with the primary internal web server at 10.1.0.20. That server is a gold mine of information about the organization. Sendai sifts through new employee manuals, news pages, employee mailing list archives, and more. In one mailing list post, a quality assurance engineer asks developers to try and reproduce a problem on the qa-sol1 machine. The password to the qa role account is buserror, he helpfully adds.
Sendai moves quickly to try this sensitive information. He scans qa-sol1 and finds that the Telnet and ssh services are available. It would be simple to Telnet into the proxy and then issue the CONNECT command himself to log into the telnetd on qa-sol1, but Sendai cannot bear to do that. He wants to connect more securely, using ssh. Sendai downloads an HTTP proxy shared library to Psyche, which allows normal applications to work transparently through the webpxy.cols.disa.mil proxy server. With that in place, Sendai makes an ssh connection to qa-sol1 and successfully logs in as qa. The system is running Solaris 8 and has quite a few users logged on. Sendai immediately reads /etc/passwd and finds that the first line consists of “+::0:0:::”. This means the system is using NIS (formerly called YP) to share accounts and configuration information among the whole department. NIS is wonderful from Sendai's perspective. It makes obtaining usernames and password hashes trivial using the ypcat command.
Obtaining the Password File from NIS
qa-sol1> ypcat passwd root:lCYRhBsBs7NcU:0:1:Super-User:/:/sbin/sh daemon:x:1:1::/: bin:x:2:2::/usr/bin: sys:x:3:3::/: adm:x:4:4:Admin:/var/adm: lp:x:71:8:Line Printer Admin:/usr/spool/lp: uucp:x:5:5:uucp Admin:/usr/lib/uucp: smmsp:x:25:25:SendMail Message Submission Program:/: listen:x:37:4:Network Admin:/usr/net/nls: nobody:x:60001:60001:Nobody:/: jdl:mY2/SvpAe82H2:101:100:James Levine:/home/jdl:/bin/csh david:BZ2RLkbD6ajKE:102:100:David Weekly:/home/david:/bin/tcsh ws:OZPXeDdi2/jOk:105:100:Window Snyder:/home/ws:/bin/tcsh luto:WZIi/jx9WCrqI:107:100:Andy Lutomirski:/home/luto:/bin/bash lance:eZN/CfM1Pd7Qk:111:100:Lance Spitzner:/home/lance:/bin/tcsh annalee:sZPPTiCeNIeoE:114:100:Annalee Newitz:/home/annalee:/bin/tcsh dr:yZgVqD2MxQpZs:115:100:Dragos Ruiu:/home/dr:/bin/ksh hennings:5aqsQbbDKs8zk:118:100:Amy Hennings:/home/hennings:/bin/tcsh [Hundreds of similar lines]
With these hundreds of password hashes in hand, Sendai goes to work on cracking them. He starts up John the Ripper on every one of his reasonably modern home machines. Each machine handles a subset of the accounts, which Sendai has sorted by crypt(3) seed (the first two characters of the hash) for efficiency. Within five minutes, dozens of the easiest passwords have been cracked. Then the rate slows down, and Sendai decides to sleep on it.
The next morning, nearly a third of the accounts have been cracked. Sendai is hoping that at least one of the users has an account on infowar using the same password. From qa-sol1, Sendai tries repeatedly to ssh into infowar, trying each cracked account in turn. The attempt fails time after time and eventually he runs out of cracked accounts. Sendai will not give up so easily. After 24 more hours, he has cracked almost half the accounts and tries ssh again. This time, he gets in using the account bruce! This is a Linux box, so Sendai tries the brk() exploit that was so successful against Psyche. No luck. He spends a couple hours trying other techniques in vain. Then he slaps himself on the forehead upon realizing that bruce is authorized to execute commands as root in the /etc/sudoers file. Sendai simply types sudo vi /etc/resolve.conf, as if he planned to edit an administrative file. Then he breaks out of vi to a root shell by issuing the command :sh. Game over! Shrax is promptly installed.
Bursting with pride and looking forward to a wallet bursting with green, Sendai composes an e-mail to Knuth's e-mail address at Hushmail.com. He describes the systems and how to access them via the Shrax client. An encrypted version of Shrax has been posted on a free Geocities Web page that Sendai just created. He then obtains Knuth's PGP key from a public keyserver and verifies that the fingerprint matches what Knuth gave him. A couple minutes later the encrypted and signed document is waiting for Knuth in his inbox.
Triumph and New Toys
The next morning, Sendai wakes up to find a glorious e-mail from PayPal notifying him of a large deposit. Knuth keeps his word, and quickly too! Sendai browses to eBay, pricing huge LCD monitors and Apple PowerBooks. These are a good way to blow a bunch of money and have something to show for it, unlike his Fiasco investment. Sendai is bidding on a 17” laptop when Knuth calls. He has already tried out Shrax and verified that the machines were fully compromised as promised. Suddenly Knuth drops a bomb, mentioning that it is now time to “start the real work.” Sendai is speechless. He spent weeks of nonstop effort to own those machines. What is Knuth saying? Apparently Knuth has no interest in those boxes at all. They were just a test to insure that Sendai is expertly skilled and reliable. “You passed with flying colors,” Knuth offers in an unsuccessful attempt to restore Sendai's pride. He notes that those machines would make a great Shrax proxy chain for safely owning the primary targets. Sendai highly approves of that idea. It should allay his constant fear of being caught, and also brings value to all of his recent efforts.
Sendai accepts the next assignment and Knuth starts rattling off the new targets. Unlike the crazy assortment last time, these all belong to banks with a heavy African presence. They include the Amalgamated Banks of South Africa, Stanbic Nigeria, Nedbank, and Standard Bank of South Africa. Knuth wants numerous machines compromised with a covert Shrax install, as well as network maps to better understand the organizations. Knuth will apparently be doing the dirty work, as Sendai need only document the access methods and leave.
“This is so much better than working at that accounting firm,” Sendai thinks as he begins his first of many successful and lucrative bank intrusions.
The End
If you enjoyed this chapter, you may opt to buy the whole book at Amazon (save $17) for 9 other chapters. My favorites are FX's chapter on SAP exploitation by a sexy hackse named h3X, Jay Beale's guide to hacking a university's student records database, and Joe Grand's phone phreaking escapades.
[1] Your humble author is a Honeynet Project member.
[2] Kernel module injection on Linux and Solaris is described at http://www.phrack.org/show.php?p=61&a=10.
[3] The KeyGhost is only one of many such products easily available over the Internet. The KEYKatcher is another popular choice.
